The Bright Horizon For Information Security Jobs
With graduation season upon us, new graduates entering the workforce are understandably anxious about their future employment. However, at least one group is poised to take advantage of a market suffering from a massive skills shortage: cybersecurity professionals.
The Bureau of Labor Statistics’ Occupational Outlook Handbook projects the demand for information security professionals will increase by 100,000 jobs in the next seven years. That need will only increase in the coming years as cybercrime continues to prove more lucrative.
The outlook for this fortunate group of new college graduates is promising. However, organizations planning to hire from this talent pool should fully understand the associated challenges.
Any effective security team requires technical members with a broad set of backgrounds and skill sets, often delineated into “Tier 1” and “Tier 2” groups. Tier 1 members generally provide a first line of review or response, and handle the most basic functions from the security team’s task lists. These tend to include following pre-determined response procedures such as virus removal, automated system restoration, or escalating the more suspicious events for further review.
Tier 2 members have more real-world experience with those escalations – the events that don’t meet pre-determined conditions. Their practical background helps to quickly weed out a false positive event or determine whether a particular observation is “wrong.”
This real-world experience is the core differentiation between a Tier 1 and Tier 2 team member – and it can only be gained over time. Granted, advanced degrees and sound technical certifications can help to establish professional credibility, but there is no substitute for real-world experience.
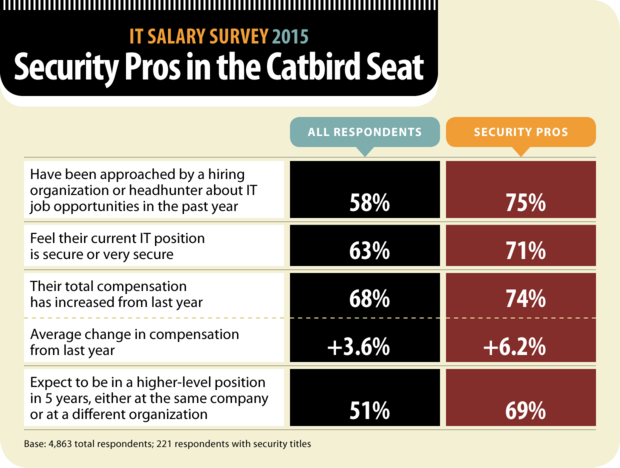
Unfortunately, Tier 2 team members are becoming increasingly difficult to hire and retain. The federal government announced its intent to fill 3,000 cybersecurity positions, but the talent pool they share with industry is a finite resource that is already under-filled. Many of these governmental positions are at the top of the federal pay ranges, further driving salary expectations for an experienced security professional to a level that is not viable for many organizations.
Organizations are faced with several options — none of which are ideal. They may attempt to hire a large group of Tier 1 team members, but considering the pending talent shortage, this is a challenge at best. Even if they manage to outfit their teams with a large group of new hires, such a team requires the guidance and tutelage of more experienced technical team members at Tier 2 to be effective.
Another method some organizations use to alleviate the strain on personnel is to use so-called automated solutions to supplement a sparse security team. Despite bold vendor claims, such solutions require trained professionals to effectively deploy and operate. Many also prefer to over-notify the operators to avoid “missing” a critical event. This often leads to alert fatigue, in which too many alerts lead to missing the small fraction that actually require attention.
Retaining top talent is the simplest solution but can be the most expensive. As demand grows across the employment force, competitive salaries will rise faster than most organizations can support. Management must find creative ways to encourage retention without relying solely on salary and other easy perks.
Job progression opportunities are a key mechanism. An employee who sees a future with their current company is less likely to seek employment elsewhere. Investment in workforce development is another method. Establishing a fair and practical training budget shows employees they can continue career progression in a company that values their professional development. There are many other options in this area, but salary alone is rarely a practical solution to foster retention.
Whether building a team from scratch, back-filling vacancies left through attrition, or supporting a broader security mission by augmenting an existing team, hiring talent is a necessity for any organization. Bringing any new talent onto the team is a challenge. Recruiters and hiring managers must effectively screen candidates for technical skills and placement onto an existing team.
Evaluating Tier 1 candidates has recently been eased somewhat by the establishment of undergraduate degree programs that focus specifically on information security. Many of these programs are still in their infancy, and have yet to be proven in the workplace.
After selecting a candidate, there is an acclimation period before a new employee is contributing at their full potential. This may involve formal and on-the-job training, a gradual ramp-up period for the new hire’s workload, and other production-limiting factors.
The demand for top security talent will continue to increase for the foreseeable future. While this is certainly welcome for recent graduates in security-focused degree programs, the need for real-world experience can only be acquired over time.


























