Stegosploit Hidden Image Code is the Future of Online Attacks
The security researcher Saumil Shah from Net Square security has presented at Hack In The Box conference in Amsterdam his Stegosploit project which allows an attacker to embed executable JavaScript code within an image to trigger a drive-by download.
The Stegosploit digital steganography project could open new scary scenarios for Internet users that could be infected by viewing a picture on any website, even without clicking on it or downloading it. The image could be the container for the priming of the malware. Shah has no doubts, Stegosploit could be the future of online attacks.
When an Internet user views the image, the hidden script would automatically load on the host the malicious code that could be used for various purposes, including control victim’s device and steal sensitive data.
The expert highlighted that antivirus software and malware detection solutions are not able to detect the Stegosploit leaving users open to any kind of attack.
Steganography was previouslyy exploitedby malware authors to hide information used by their malicious codes (i.e. C&C addresses or botnet parameters), but as Shah explained “Stegosploit” tool Shah takes the stenographic approach to a new level where exploits are delivered not only in plain sight, but also “with style.”
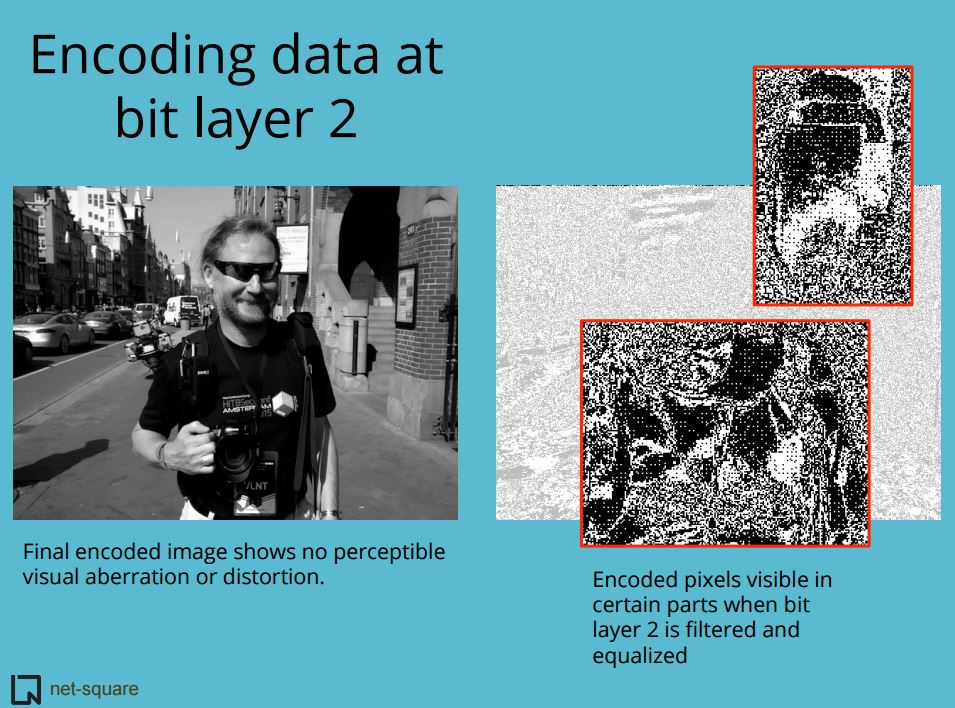
Shah has worked on Stegosploit technique to hide executable code within an image and execute the same code in a web browser supporting HTML 5 Canvas. The expert exploits HTML5 CANVAS to read image pixel data using Java Script and decode the image within the browser.
Shah demonstrated Stegosploit for the first time in March at the SyScan, initially the hacking technique required using two distinct images respectively to contain the executable code and code to decode it. Further efforts in the research on Stegosploit allowed its improvement, Shah succeeded to embed both the executable code and the decoder within the same image (PNG and JPEG).
Security firms are not aware of cases of this Stegosploit technique being used in the wild, but they fear that it will become soon a scaring reality.
Security Affairs: http://bit.ly/1KeTvkB


























