Predictions for cyber-crime in 2015 and how the Security Industry is Responding
From Heartbleed and Shellshock to the Target breach and the Sony hack, last year was littered with high-profile cyber threats and security breaches.
The dire consequences an attack can have on a business have become increasingly apparent, as poor response to security breaches has led to the resignation of senior staff and even companies going out of business.
In 2015, the frequency and severity of cyber-attacks will continue to increase – and organisations will have to explore new approaches in responding to cyber-attacks. These are my predictions on how cybercrime will manifest itself this year, and how the cyber-security industry will develop in response.
Each year, the frequency and severity of cyber-attacks increases, and there is no reason to think that 2015 will buck this trend.
Europe may appear to be relatively unscathed so far, but this is probably because public disclosure is not generally required as it is in the US. In 2015, however, there will be an attack on the scale of the Target breach – so large and far reaching that it can't be swept under the carpet. The consequence will be harsher measures imposed on companies within the EU who are not adequately prepared for security breaches. And, as in the US, it's possible we will see CSOs or even CEOs lose their jobs as a result.
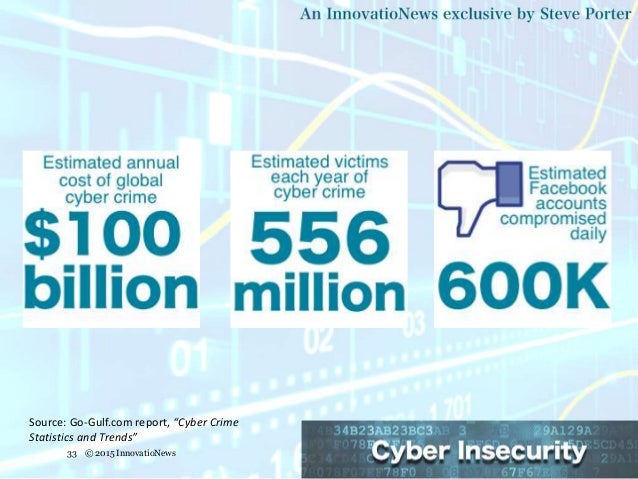
Cybercrime will continue to boom in 2015, and we'll see even more eager criminals enter the profession.
The reason for this is simple: cybercrime pays, and the rewards heavily outweigh the risks.
This is not because there aren't harsh punishments for those who are caught. And harsh-punishments being handed-out, is proven by Albert Gonzalez the TJX attack mastermind. He is still serving a twenty years sentence for his cyber crimes. However the problem is because the likelihood of being caught is very small in comparison to other serious crimes.
Furthermore, there is a very low cost of entry for cybercriminals – the tools needed to attack even the most comprehensive security systems are incredibly cheap when compared to what could be gained.
Until cybercrime is less rewarding, this trend is likely to continue.
In 2015 organisations will finally begin to realise that there is no silver bullet for cyber-security – yet another shiny security technology won't save us (just as the last ones didn't).
Rather than continuing to focus resources on prevention and detection, firms will focus attention on response and developing resilience – the ability to weather the inevitable incidents as just another part of doing business.
The SandWorm zero-day exploit made big headlines when its discovery was revealed in October of last year – partially because of the technical implications, but also because of the impact. At least one hacking group used the vulnerability to target critical infrastructure, a trend that will continue in 2015.
Although hactivism failed to dominate the headlines in 2014, it has always been cyclical. With several conflicts persisting around the world, and given a controversial general election this year in the UK, we should expect renewed momentum in this kind of malicious activity.
Threat intelligence and threat knowledge-sharing shows growing promise, representing a real opportunity to turn the tables on the bad guys. But there are a number of obstacles to its success, including the relative quality of the data involved and how complicated it can be to share.
In 2015 we will see improvements here, particularly with the work that NIST is doing in the U.S. We also expect the ISO to release some Incident Response Management guidelines this year.
We've learnt by now that technology is no panacea. Therefore getting the balance of how humans and machines work together will be increasingly important.
Studies of chess masters and supercomputers have shown that a computer alone, no matter how powerful, can still be overcome. Indeed the best approach teams up good chess players with a computer. This same approach can and will be applied to security –particularly incident response.
Security solutions still lack the judgement needed to ensure the cure prescribed isn't worse than the disease it's intended to address. The ideal approach will leverage computers for information collection and analysis, but rely on humans to fine-tune the response.
Techradar: http://bit.ly/1y2tuKQ


























