New Case Highlights Deep Hole in Cyber Insurance
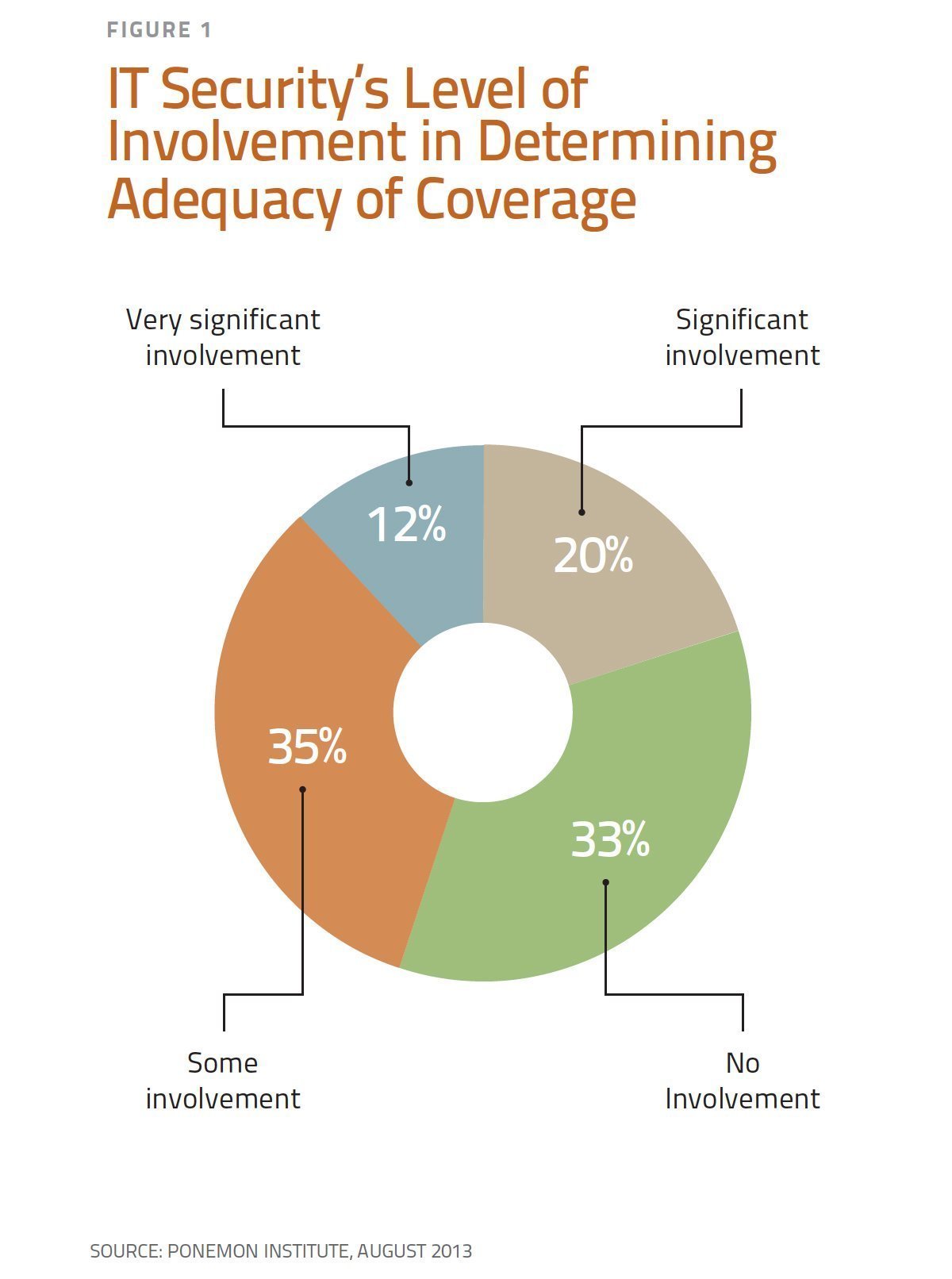
IT security's level of involvement in determining adequacy of insurance coverage
Insurance policies covering data breach liability began appearing roughly ten years ago. We noted then a troublesome provision in some forms that seemed to exclude coverage for the insured’s failure to maintain data security – in other words, the very risk the insured was seeking to insure. We’ll call it the “Mistake Exclusion.” One AIG form from 2006, for example, excluded coverage arising out of “your failure to take reasonable steps to use, design, maintain and upgrade your security.” A 2009 Darwin form excluded coverage for any claim arising out of “any failure of an Insured to continuously implement the procedures and risk controls identified in the Application for this insurance.” But isn’t liability insurance supposed to do just that – protect against the insured’s mistakes, innocent or negligent? We hoped and expected that as the market for these policies matured, savvy brokers and risk managers would insist that these Mistake Exclusions be removed or substantially narrowed. But that has not happened.
We now have the first case we are aware of by an insurer seeking to enforce a Mistake Exclusion. In Columbia Casualty Company v. Cottage Health Systems, filed May 7, 2015 in the U.S. District Court in Los Angeles, Columbia seeks to enforce an exclusion barring coverage for a data breach claim arising out of any “failure of an Insured to continuously implement the procedures and risk controls identified in the Insured’s application for this Insurance and all related information submitted to the Insurer in conjunction with such application whether orally or in writing.” Columbia’s complaint arises out of a class action suit against Cottage alleging that, for a period of two months in 2013, 32,500 patient records were accessible via the Internet. Cottage had hired a third-party vendor to store Cottage’s records electronically and that vendor mistakenly set the File Transfer Protocol settings to allow public access. Columbia funded Cottage’s defense and settlement, but is suing to recover all of its payments from Cottage.
Imagine that you’re Cottage. You bought an insurance policy against data breach claims, only to find out that what you bought was a lawsuit by your insurer to establish that your mistake, even an innocent one, caused the data breach. That’s not insurance. That’s a knife in the back.
Columbia might prevail in this lawsuit. It relies on language that appears not just in an exclusion, but also in a “condition precedent” to coverage. On the other hand, a court could decide that the exclusion effectively renders any coverage a nullity and should be disregarded. Or the court could read an implied “unreasonable failure” standard into the exclusion to meet the insured’s expectations. Even then, however, the insured still risks a lawsuit from its own insurer in most cases. And that risk becomes a hammer in the hands of an insurer seeking to limit its payout. At bottom, Columbia really only seems to want to insure against a criminal hacker attack that beats the best security system money can buy. But if that’s so, it could have said that easily enough.
Columbia’s and other insurers’ Mistake Exclusions underscore just how immature the cyber insurance market still is. They reflect insurers’ lack of confidence in their ability to underwrite cyber risks, motivating them to try to shift that very risk back onto their insured. A similar dynamic took place in the nascent market for technology errors and omissions policies. Eventually, though, insurers realized that they could rely on their insureds’ own competitive need for quality control and claim mitigation procedures to control the risk of claims for defective products. The same is now becoming true regarding cyber security. Virtually every business recognizes that the monetary and reputational costs that result from failing to protect electronic information are too high not to adopt state-of-the-art security measures. Insurers should now be in a position to underwrite confidently without having to ask their insureds to re-insure them.
Fortunately, insureds have been successful in demanding that the Mistake Exclusion be removed from their policies where it appears. Brokers and risk managers therefore can and should take steps to avoid this trap for the unwary.
JD Supra: http://bit.ly/1CA8Xqp


























