Hackers Invade Hospital Networks
The TrapX report, “Anatomy of an Attack–Medical Device Hijack (MEDJACK),” describes in detail three situations in which hackers were able to get into supposedly secure hospital networks, collecting valuable information, by targeting medical devices.
Once into the devices, the hackers were able to roam at will through hospital networks. Their goal was the valuable health insurance information in patient records—this, TrapX stated, is worth 20 times the value of a credit card record on the black market. But had they wanted to, they could potentially have taken control of the devices themselves. Here are the three incidents detailed in the TrapX report.
- A hospital where researchers discovered that three blood gas analyzers in the laboratory contained backdoors into the hospital network, and records were being sent to an unknown location in Europe;
- A hospital where hackers infected a Picture Archive and Communications System (PACS) in the hospital radiology department and then, using the PACS system, were able to move through that network collecting information and sending it Guiyang, China;
- A hospital where hackers installed a back door in X-ray equipment.
From the compromised system, hackers were able to move through that network extracting information. How could this happen?
After all, the products we were creating were not being connected to a worldwide network of computers that anyone could access. In 1984, the Internet was barely in its infancy and not used by the general public (the first commercial dial-up Internet Service Provider was formed in 1990); the World Wide Web (1991) had yet to be invented. Our systems were secure, because they would operate in isolation. It was an appropriate design choice at the time.
So the world has changed, but many medical devices and systems have not. The basic software architecture of many of the devices used in hospitals and medical clinics today is still based on designs from 10 or 20 years ago. The software may have been updated to support graphical or touchscreen user interfaces, enable greater connectivity to IT networks and increase ease-of-use, but security has rarely been a priority when building new versions of these old designs.
Over the past 25 years the automotive industry has made tremendous progress in vehicle safety. When I was child, seatbelts were the primary safety feature in most cars. Today cars are designed to withstand collisions at even high speeds. Anti-lock brakes, airbags and a host of other safety features are standard and automakers continue to invest heavily in improving safety.
These advances are the result of automakers embracing safety as a fundamental design principal and making heavy investments into safety. It is time for medical device companies to follow suit and treat security as a fundamental design component, not an optional add-on. It is no longer sufficient to refresh old versions of products with a few new features. New platforms and architectures must be adopted that incorporate security into the every level of product design from selection of hardware platforms through application implementation.
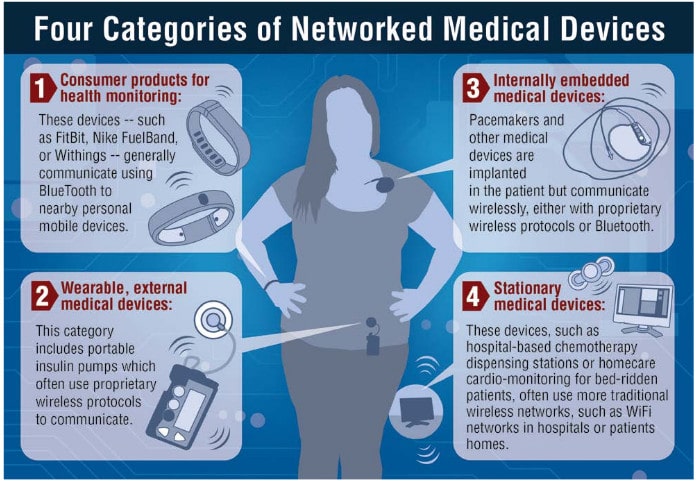
As the MedJack report shows, any insecure medical device, whether it is preforming a critical function or not, can be targeted by hackers. Once compromised, they can then be used as a beachhead to penetrate more deeply into medical networks. Security must be considered a critical component of all devices, even those performing seemingly insignificant tasks. And that includes implanted medical devices, as the University of Michigan’s Kevin Fu points out here, just because they are inside your body, they are not invulnerable.
Building security into new devices is critical to ensure the next generation of medical devices does not suffer from the security problems outlined in the MedJack report. But a larger problem still exists. There are millions of legacy devices with weak or non-existent security in use today. The cost to replace these devices would run into the hundreds of billions of dollars. Realistically, it will take a decade or more to replace all of these devices.
A cost-effective alternative is needed for these systems. One option is a low cost bump-in-the-wire (BITW) security device. Such a device can be installed in front of a legacy device and used to control all network communication with the device. I describe that approach in more detail in “How to Build a Safer Internet of Things” published in IEEE Spectrum earlier this year.
The report proves that medical devices are being targeted by cybercriminals. Stopping these attacks will require a change of mindset by everyone involved in using and developing medical devices. Much like the auto industries approach to safety, this will require a long-term commitment and a “security first” mindset.
IEEE: http://bit.ly/1QFrk3k


























